With the passage into law of the iniquitous Investigatory Powers (IP) Bill in the UK at the end of November last year, it is way past time for all those who care about civil liberties in this country to exercise their right to privacy.
The new IP Act permits HMG and its various agencies to surveil the entire online population. The Act actually formalises (or in reality, legalises) activity which has long gone on in this country (as in others) in that it gives LEAs and others a blanket right of surveillance.
The Act (PDF) itself states that it is:
“An Act to make provision about the interception of communications, equipment interference and the acquisition and retention of communications data, bulk personal datasets and other information; to make provision about the treatment of material held as a result of such interception, equipment interference or acquisition or retention; to establish the Investigatory Powers Commissioner and other Judicial Commissioners and make provision about them and other oversight arrangements; to make further provision about investigatory powers and national security; to amend sections 3 and 5 of the Intelligence Services Act 1994; and for connected purposes.”
(Don’t you just love the “connected purposes” bit?)
The Open Rights Group says the Act:
“is one of the most extreme surveillance laws ever passed in a democracy. Its impact will be felt beyond the UK as other countries, including authoritarian regimes with poor human rights records, will use this law to justify their own intrusive surveillance regimes.”
Liberty, which believes the Act breeches the public’s rights under the Human Rights Act, is challenging the Act through the Courts. That organisation says:
“Liberty will seek to challenge the lawfulness of the following powers, which it believes breach the public’s rights:
– Bulk hacking – the Act lets police and agencies access, control and alter electronic devices like computers, phones and tablets on an industrial scale, regardless of whether their owners are suspected of involvement in crime – leaving them vulnerable to further attack by hackers.
– Bulk interception – the Act allows the state to read texts, online messages and emails and listen in on calls en masse, without requiring suspicion of criminal activity.
– Bulk acquisition of everybody’s communications data and internet history – the Act forces communications companies and service providers to hand over records of everybody’s emails, phone calls and texts and entire web browsing history to state agencies to store, data-mine and profile at its will.
This provides a goldmine of valuable personal information for criminal hackers and foreign spies.
– “Bulk personal datasets” – the Act lets agencies acquire and link vast databases held by the public or private sector. These contain details on religion, ethnic origin, sexuality, political leanings and health problems, potentially on the entire population – and are ripe for abuse and discrimination.”
ProtonMail, a mail provider designed and built by “scientists, engineers, and developers drawn together by a shared vision of protecting civil liberties online.” announced on Thursday 19 January that they will be providing access to their email service via a Tor onion site, accessible only over the Tor anonymising network. The ProtonMail blog entry announcing the new service says:
“As ProtonMail has evolved, the world has also been changing around us. Civil liberties have been increasingly restricted in all corners of the globe. Even Western democracies such as the US have not been immune to this trend, which is most starkly illustrated by the forced enlistment of US tech companies into the US surveillance apparatus. In fact, we have reached the point where it simply not possible to run a privacy and security focused service in the US or in the UK.
At the same time, the stakes are also higher than ever before. As ProtonMail has grown, we have become increasingly aware of our role as a tool for freedom of speech, and in particular for investigative journalism. Last fall, we were invited to the 2nd Asian Investigative Journalism Conference and were able to get a firsthand look at the importance of tools like ProtonMail in the field.
Recently, more and more countries have begun to take active measures to surveil or restrict access to privacy services, cutting off access to these vital tools. We realize that censorship of ProtonMail in certain countries is not a matter of if, but a matter of when. That’s why we have created a Tor hidden service (also known as an onion site) for ProtonMail to provide an alternative access to ProtonMail that is more secure, private, and resistant to censorship.”
So, somewhat depressingly, the UK is now widely seen as a repressive state, willing to subject its citizens to a frighteningly totalitarian level of surveillance. Personally I am not prepared to put up with this without resistance.
Snowden hype notwithstanding, HMG does not have the resources to directly monitor all electronic communications traffic within the UK or to/from the UK, so it effectively outsources that task to “communications providers” (telcos for telephony and ISPs for internet traffic). Indeed, the IP act is intended, in part, to force UK ISPs to retain internet connection records (ICRs) when required to do so by the Home Secretary. In reality, this means that all the major ISPs, who already have relationships with HMG of various kinds, will be expected to log all their customer’s internet connectivity and to retain such logs for so long as is deemed necessary under the Act. The Act then gives various parts of HMG the right to request those logs for investigatory purposes.
Given that most of us now routinely use the internet for a vast range of activity, not limited just to browsing websites, but actually transacting in the real world, this is akin to requiring that every single library records the book requests of its users, every single media outlet (newsagents, bookshops, record shops etc.) records every purchase in a form traceable back to the purchaser, every single professional service provider (solicitors, lawyers, doctors, dentists, architects, plumbers, builders etc.) record all activity by name and address of visitor. All this on top of the already existing capability of HMG to track and record every single person, social media site or organisation we contact by email or other form of messaging.
Can you imagine how you would feel if on every occasion you left your home a Police Officer (or in fact officials from any one of 48 separate agencies, including such oddities as the Food Standards Agency, the NHS Business Services Authority or the Gambling Commission) had the right, without a warrant or justifiable cause, to stop you and search you so that (s)he could read every piece of documentation you were carrying? How do you feel about submitting to a fishing trip through your handbag, briefcase, wallet or pockets?
I have no problem whatsoever with targeted surveillance, but forgive me if I find the blanket unwarranted surveillance of the whole populace, on the off-chance it might be useful, completely unacceptable. What happened to the right to privacy and the presumption of innocence in the eyes of the law? The data collected by ISPs and telcos under the IP act gives a treasure trove of information on UK citizens that the former East German Stasi could only have dreamed about.
Now regardless of whether or not you trust HMG to use this information wisely, and only for the reasons laid out under the Act, and only in the strict circumstances laid out in the Act, and only with the effective scrutiny of “independent” oversight, how confident are you that any future administration would be similarly wise and circumspect? What is to stop a future, let us suppose, less enlightened or liberal administration, misusing that data? What happens if in future some act which is currently perfectly legal and permissible, if of somewhat dubious taste, morality and good sense (such as, say, reading the Daily Mail online) were to become illegal? What constraint would there be to prevent a retrospective search for past consumers of such dubious material in order to flag them as “persons of interest”?
And even if you are comfortable with all of that, how comfortable are you with the idea that organised crime could have access to all your personal details? Given the aggregation of data inherent in the requirement for bulk data collection by ISPs, those datasets become massive and juicy targets for data theft (by criminals as as well as foreign nation states). And if you think that could not happen because ISPs and Telcos take really, really, really good care of their customer’s data, then think about TalkTalk or Plusnet or Three or Yahoo.
And they are just a few of the recent ones that we /know/ about.
So long as I use a UK landline or mobile provider for telephony, there is little I can do about the aggregation of metadata about my contacts (and if you think metadata aggregation doesn’t matter, take a look at this EFF note). I can, of course, and do, keep a couple of (cash) pre-paid SIM only mobile ‘phones handy – after all, you never know when you may need one (such as perhaps, in future when they become “difficult” to purchase). And the very fact that I say that probably flags me as suspicious in some people’s minds. (As an aside, ask yourself what comes to mind when you think about someone using a cash paid, anonymous, second hand mobile ‘phone. See? I must be guilty of something. Notice how pernicious suspicion becomes? Tricky isn’t it?) Nor can I do much about protecting my email (unless I use GPG, but that is problematic and in any case does not hide the all important metadata in the to/from/date/subject headers). Given that, I have long treated email just as if it were correspondence by postcard, though somewhat less private. For some long time I used to routinely GPG sign all my email. I have stopped doing that because the signatures meant, of course, that I had no deniability. Nowadays I only sign (and/or encrypt) when I want my correspondents to be sure I am who I say I am (or they want that reassurance).
But that does not mean I think I should just roll over and give up. There is plenty I can do to protect both myself and my immediate family from unnecessary, intrusive, unwarranted and unwanted snooping. For over a year now I have been using my own XMPP server in place of text messaging. I have had my own email server for well over a decade, and so long as I am conversing there with others on one of my domains served by that system, then that email is pretty private too (protected in transit by TLS using my own X509 certificates). My web browsing has also long been protected by Tor. But all that still leaves trails I don’t like leaving. I might, for example, not want my ISP to even know that I am using Tor, and in the case of my browsing activity it becomes problematic to protect others in my household or to cover all the multiple devices we now have which are network connected (I’ve actually lost count and would have to sit down and list them carefully to be sure I had everything covered).
What to do? The obvious solution is to wrap all my network activity in a VPN tunnel through my ISP’s routers before I hit the wider internet. That way my ISP can’t log anything beyond the fact that I am using a VPN. But which VPN to use? And should I go for a commercial service or roll my own? Bear in mind that not all VPNs are created equal, nor are they all necessarily really private or secure. The “P” in VPN refers to the ability to interconnect two separate (probably RFC 1918) private networks across a public untrusted network. It does not actually imply anything about the end user’s privacy. And depending upon the provider chosen and the protocols used, end user privacy may be largely illusory. In the worst case scenario, depending upon the jurisdiction in which you live and your personal threat model, a badly chosen VPN provider may actually reduce privacy by drawing attention to the fact that you value that privacy. (As an aside, using Tor can also have much the same effect. Indeed, there is plenty of anecdotal evidence to suggest that Tor usage lights you up like a christmas tree in the eyes of the main GPAs.)
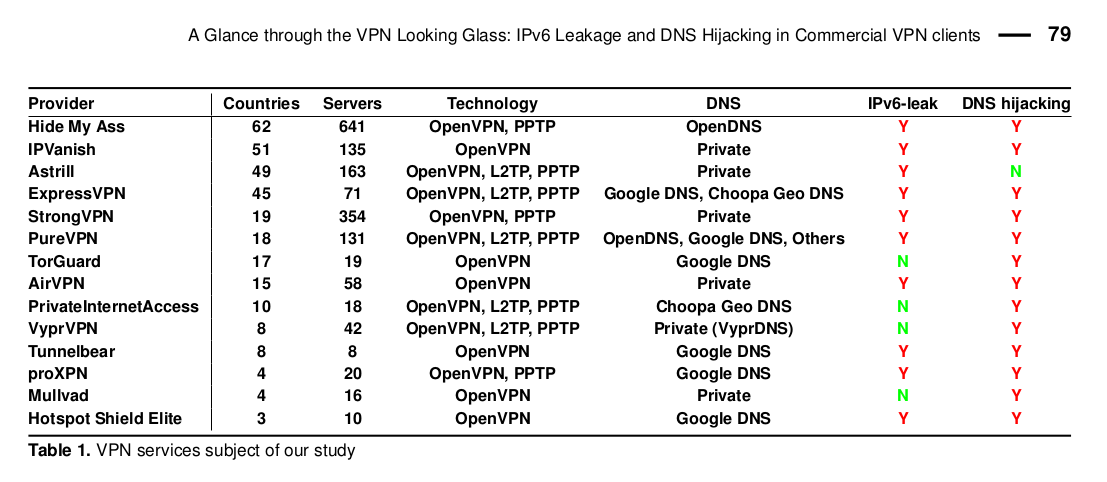
Back in 2015, a team of researchers from the Sapienza University of Rome and Queen Mary University of London published a paper (PDF) entitled “A Glance through the VPN Looking Glass: IPv6 Leakage and DNS Hijacking in Commercial VPN clients”. That paper described the researcher’s findings from a survey of 14 of the better known commercial VPN providers. The teams chose the providers in much the same way you or I might do so – they searched on-line for “best VPN” or “anonymous VPN” and chose the providers which came highest or most frequently in the search results. The paper is worth reading. It describes how a poor choice of provider could lead to significant traffic leakage, typically through IPV6 or DNS. The table below is taken from their paper.
The paper describes some countermeasures which may mitigate some of the problems. In my case I disable IPV6 at the router and apply firewall rules at both the desktop and VPS end of the tunnel to deny IPV6. My local DNS resolver files point to the OpenVPN endpoint (where I run a DNS resolver stub) for resolution and both that server and my local DNS resolvers (dnsmasq) point only to opennic DNS servers. It may help.
There are reports that usage of commercial VPN providers has gone up since the passage of the IP act. Many commercial VPN providers will be using the passage of the act as a potential booster for their services. And there are plenty of VPN providers about – just do what the Sapienza and Queen Mary researchers did and search for “VPN Provider” or “VPN services” to get lots of different lists, or take a look at lists provided by such sites as PrivacyTools or BestVPN. One useful point about the better commercial providers is that they usually have substantial infrastructure in place offering VPN exit points in various geographic locations. This can be particularly useful if you want to appear to be based in a particular country. Our own dear old BBC for example will block access to some services if you are not UK based (or if you are UK based and try to access services designed for overseas users). This can be problematic for UK citizens travelling overseas who wish to view UK services. A VPN with a UK exit gets around that problem. VPN users can also use local exits when they wish to access similarly (stupidly) protected services in foreign locales (the idiots in the media companies who are insistent on DRM in all its manifest forms are becoming more than just tiresome).
Some of the commercial services look better than others to me, but they all have one simple flaw as far as I am concerned. I don’t control the service. And no matter what the provider may say about “complete anonymity” (difficult if you want to pay by credit card) or “no logs”, the reality is that either there will be logs or the provider may be forced to divulge information by law. And don’t forget the problem of traffic leakage through IPV6 or DNS noted above. One further problem for me in using a commercial VPN provider rather than my own endpoint(s) is that I cannot then predict my apparent source IP address. This matters to me because my firewall rules limit ssh access to my various servers by source IP address. If I don’t know the IP address I am going to pop out on, then I’m going to have to relax that rule. I choose not to. I have simply amended my iptables rules to permit access from all my VPN endpoints.
The goldenfrog site has an interesting take on VPN anonymity. (Note that Goldenfrog market their own VPN service called “VyprVPN” so they are not entirely disinterested observers, but the post is still worth reading nevertheless). If you are simply concerned with protecting your privacy whilst browsing the net, and you are not concerned about anonymity then there may be a case for you to consider using a commercial provider – just don’t pick a UK company because they will be subject to lawful intercept requests under the IP act. Personally I’d shy away from US based companies too, (a view that is shared by PrivacyTools.io so it’s not just me). I would also only pick a provider which supports OpenVPN (or possibly SoftEther) in preference to less secure protocols such as PPTP, or L2TP. (For a comparison of the options, see this BestVPN blog post.
If you wish to use a commercial VPN provider, then I would strongly recommend that you pay for it – and check the contractual arrangements carefully to ensure that they match your requirements. I suggest this for the same reasons I recommend that you pay for an email service. You get a contract. In my view, using a free VPN service might be worse than using no VPN. Think carefully about the business model for free provision of services on the ‘net. Google is a good example of the sort of free service provider which I find problematic. Using a commercial, paid for, VPN service has the distinct advantage that the provider has a vested interest in keeping his clients’ details, and activity, private. After all, his business depends upon that. Trust is fragile and easily lost. If your business is predicated on trustworthiness then I would argue that you will (or should) work hard to maintain that trust. PrivacyTools has a good set of recommendations for VPN providers.
But what if, like me, you are still unsure about using a commercial VPN? Should you use your own setup (as I do)? Here are some things to think about.
Using a commercial VPN
| For | Against |
| Probably easier than setting up OpenVPN on a self-managed VPS for most people. The service provider will usually offer configuration files aimed at all the most popular operating systems. In many cases you will get a “point and click” application interface which will allow you to select the country you wish to pop out in. | “Easier” does not mean “safer”. For example, the VPN provider may provide multiple users with the same private key wrapped up in its configuration files. Or the provider may not actually use OpenVPN. The provider may not offer support for YOUR chosen OS, or YOUR router. Beware in particular of “binary blob” installation of VPN software or configuration files (this applies particularly to Windows users). Unless you are technically competent (which you may not be if you are relying on this sort of installation) then you have no idea what is in that binary installation. |
| You get a contract (if you pay!) | That contract may not be as strong as you might wish, or it might specifically exclude some things you might wish to see covered. Check the AUP before you select your provider. You get what you pay for. |
| Management and maintenance of the service (e.g. software patching) is handled by the provider. | You rely on the provider to maintain a secure, up to date, fully patched service. Again, you get what you pay for. |
| The provider (should) take your security and privacy seriously. Their business depends on it. | The provider may hold logs, or be forced to log activity if local LE require that. They may also make simple mistakes which leak evidence of your activity (is their DNS secure?)
The VPN service is a large, attractive, juicy target for hostile activity by organised crime and/or Global Passive Adversaries such as GCHQ and NSA. Consider your threat model and act accordingly. |
| Your network activity is “lost” in the noise of activity of others. | But your legal and legitimate activity could provide “cover” for criminal activity of others. If this results in LEA seizure (or otherwise surveillance) of the VPN endpoint then your activity is swept up in the investigation. Are you prepared for the possible consequences of that? |
| You should get “unlimited” bandwidth (if you pay for it). | But you may have to trade that off for reduced access speed, particularly if you are in contention for network usage with a large number of other users |
| You (may) be able to set up the account completely anonymously using bitcoin. | Using a VPN provider cannot guarantee you are anonymous. All it can do is enhance your privacy. Do not rely on a VPN to hide illegal activity. (And don’t rely on Tor for that either!) |
| You may be able to select from a wide range of exit locations depending upon need. | “Most VPN providers are terrible” |
Using your own VPN
| For | Against |
| You get full control over the protocol you use, the DNS servers you use, the ciphers you choose and the location(s) you pop up in. | You have to know what you are doing and you have to be comfortable in configuring the VPN software. Moreover, you need to be sure that you can actually secure the server on which you install the VPN server software as well as the client end. There is no point in having a “secure” tunnel if the end server leaks like a sieve or is subject to surveillance by the server provider – you have just shifted surveillance from the UK ISP to someone else. |
| It can be cheaper than using a commercial service. | It may not be. If you want to be able to pop out in different countries you will have to pay for multiple VPSs in multiple datacentres. You will also be responsible for maintaining those servers. |
| You can be confident that your network activity is actually private because you can enforce your own no logging policy. | No you can’t be sure. The VPS provider may log all activity. Check the privacy policy carefully. And be aware that the provider of a 3 euro a month VPS is very likely to dump you in the lap of any LEA who comes knocking on the door should you be stupid enough to use the VPN for illegal activity (or even any activity which breaches their AUP).
Also bear in mind the fact that you have no plausible deniability through hiding in a lot of other’s traffic if you are the only user of the VPN – which you paid for with your credit card. |
I’ve used OpenVPN quite a lot in the past. I like it, it has a good record for privacy and security, it is relatively easy to set up, and it is well supported on a range of different devices. I have an OpenVPN endpoint on a server on the outer screened subnet which forms part of my home network so that I can connect privately to systems when I am out and about and wish my source IP to appear to be that at my home address. This can be useful when I am stuck in such places as airport lounges, internet cafes, foreign (or even domestic) hotels etc. So when the IP Act was still but a gleam in the eyes of some of our more manic lords and masters, I set up one or two more OpenVPN servers on various VPSs I have dotted about the world. In testing, I’ve found that using a standard OpenVPN setup (using UDP as the transport) has only a negligible impact on my network usage – certainly much less than using Tor.
Apart from the privacy offered by OpenVPN, particularly when properly configured to use forward secrecy as provided by TLS (see gr3t for some tips on improving security in your configuration), we can also make the tunnel difficult to block. We don’t (yet) see many blanket attempts to block VPN usage in the UK, but in some other parts of the world, notably China or reportedly the UAE for example, such activity can be common. By default OpenVPN uses UDP as the transport protocol and the server listens on port 1194. This well known port and/or protocol combination could easily be blocked at the network level. Indeed, some hotels, internet cafes and airport lounges routinely (and annoyingly) block all traffic to ports other than 80 and 443. If, however, we reconfigure OpenVPN to use TCP as the transport and listen on port 443, then (DPI notwithstanding) to most observers its traffic becomes indistinguishable from HTTPS which makes blocking it much more difficult. There is a downside to this though. The overhead of running TCP over TCP can degrade your network experience. That said however, in my view a slightly slower connection is infinitely preferable to no connection or an unprotected connection.
In my testing, even using Tor over the OpenVPN tunnel (so that my Tor entry point appears to the Tor network to be the OpenVPN endpoint) didn’t degrade my network usage too much. This sort of Tor usage is made easier by the fact that I run my Tor client (either Tails, or Whonix) from within a virtual server instance running on one of my desktops. Thus if the desktop is connected to an OpenVPN tunnel then the Tor client is forced to use that tunnel to connect to Tor and thence the outside world.
However, this set up has a few disadvantages, not least the fact that I might forget to fire up the OpenVPN tunnel on my desktop before starting to use Tor. But the biggest problem I face in running a tunnel from my desktop is that it only protects activity /from/ that desktop. Any network connections from any of my mobile devices, my laptops, my various servers, or other network connected devices (as I said, I have lost count) or most importantly, my family’s devices, are perforce unprotected unless I can set up OpenVPN clients on them. In some cases this may be possible (my wife’s laptop for example) but it certainly isn’t ideal and in many cases (think my kid’s ‘phones for example) it is going to be completely impractical. So the obvious solution is to move the VPN tunnel entry point to my domestic router. That way, /all/ traffic to the net will be forced over the tunnel.
When thinking about this, Initially I considered using a raspberry pi as the router but my own experience of the pi’s networking capability left me wondering whether it would cope with my intended use case. The problem with the pi is that it only has one ethernet port and its broadcom chip only supports USB 2.0 connection. Internally the pi converts ethernet to USB. Since the chip is connected to four USB external ports and I would need to add a USB to ethernet conversion externally as well as USB wifi dongle in order to get the kind of connectivity I want (which includes streaming video) I fear that I might overwhelm the pi – certainly I’m pretty sure the device might become a bottleneck. However, I have /not/ tested this (yet) so I have no empirical evidence either way.
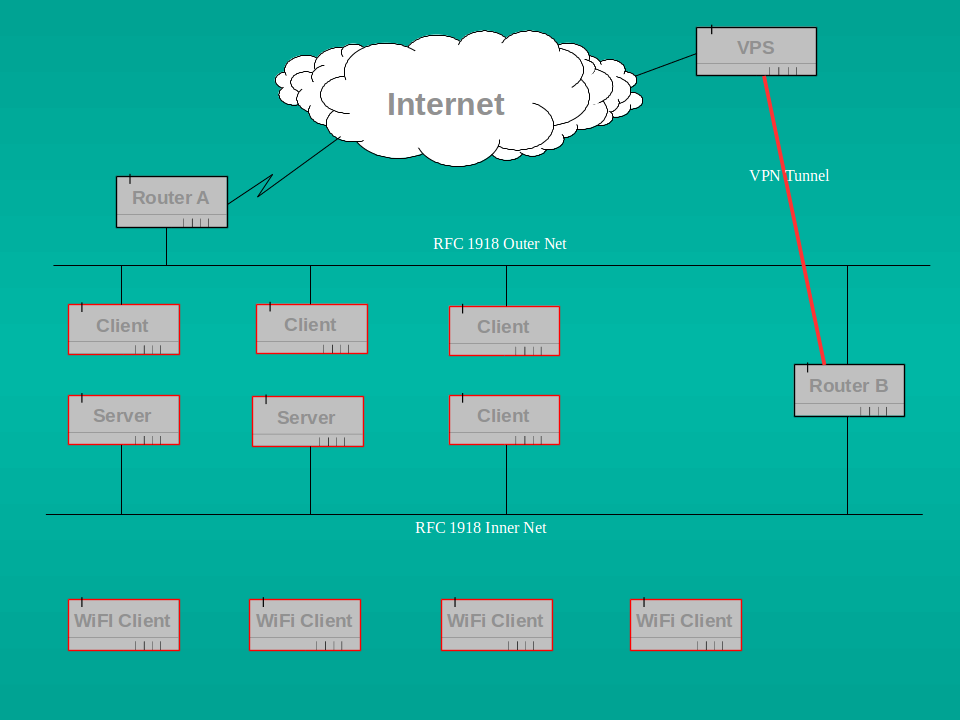
My network is already segmented in that I have a domestic ADSL router connected to my ISP and a separate, internal ethernet/WiFi only router connecting to that external router. It looks (something) like this:
Since all the devices I care most about are inbound of the internal router (and wired rather than wifi where I really care) I can treat the network between the two devices as a sacrificial screened subnet. I consider that subnet to be almost as hostile as the outside world. I could therefore add the pi to the external screened net and thus create another separate internal network which is wifi only. That wouldn’t help with my wired devices (which tend to be the ones I really worry about) but it would give me a good test network which I could use as “guest only” access to the outside world. I have commented in the past about the etiquette of allowing guests access to my network. I currently force such access over my external router so that the guests don’t get to see my internal systems. However, that means that in future they won’t get the protection offered by my VPN. That doesn’t strike me as fair so I might yet set up a pi as described (or in fact add another router, they are cheap enough).
Having discounted the pi as a possibility, then another obvious solution would be re-purpose an old linux box (I have plenty) but that would consume way more power than I need to waste and looks to be overkill so the obvious solution is to stick with the purpose built router option. Now both OpenWrt or its fork LEDE and the more controversial DD-WRT offer the possibility of custom built routers with OpenVPN client capability built in. The OpenWrt wiki has a good description of how to set up OpenVPN. The DD-WRT wiki entry somewhat is less good, but then OpenWrt/LEDE would probably be a better choice in my view anyway. I’ve used OpenWrt in the past (on an Asus WL-500g) but found it a bit flaky. Possibly that is a reflection of the router I used (fairly old, bought cheap off ebay) and I should probably try again with a more modern device. But right now it is possible to buy new, capable SOHO routers with OpenVPN capability off the shelf. A quick search for “openvpn routers” will give you devices by Asus, Linksys, Netgear, Cisco or some really interesting little devices by GL Innovations. The Gli devices actually come with OpenWRT baked in and both the GL-MT300N and the slightly better specced GL-AR300M look to be particularly useful. I leave the choice of router to you, but you should be aware that many SOHO routers have lamentably poor security out of the box and even worse security update histories. You also need to bear in mind that VPN capability is resource intensive so you should choose the device with the fastest CPU and most RAM you can afford. I personally chose an Asus device as my VPN router (and yes, it is patched to the latest level….) simply because they are being actively audited at the moment and seem to be taking security a little more seriously than some of their competitors. I may yet experiment with one of the GL devices though.
Note here that I do /not/ use the OpenVPN router as the external router connected directly to my ISP, my new router replaced my old “inside net” router. This means that whilst all the connections I really care about are tunnelled over the OpenVPN route to my endpoint (which may be in one of several European datacentres depending upon how I feel) I can still retain a connection to the outside world which is /not/ tunnelled. There are a couple of reasons for this. Firstly some devices I use actually sometimes need a UK IP presence (think streaming video from catch-up TV or BBC news for example). Secondly, I also wish to retain a separate screened sub-net to house my internal OpenVPN server (to allow me to appear to be using my home network should I so choose when I’m out and about). And of course I may occasionally just like to use an unprotected connection simply to give my ISP some “noise” for his logs….
So, having chosen the router, we now need to configure it to use OpenVPN in client mode. My router can also be configured as a server, so that it would allow incoming tunnelled connections from the outside to my network, but I don’t want that, and nor probably do you. In my case such inbound connections would in any event fail because my external router is so configured as to only allow inbound connections to a webserver and my (separate) OpenVPN server on the screened subnet. It does not permit any other inbound connections, nor does my internal router accept connections from either the outside world or the screened subnet. My internal screened OpenVPN server is configured to route traffic back out to the outside world because it is intended only for such usage.
My new internal router expects its OpenVPN configuration file to follow a specific format. I found this to be poorly documented (but that is not unusual). Here’s how mine looks (well, not exactly for obvious reasons, in particular the (empty) keys are not real, but the format is correct).
# config file for router to VPN endpoint 1
# MBM 09/12/16
client
dev tun
proto udp
remote 12.34.56.78 1194
resolv-retry infinite
nobind
user nobody
# Asus router can’t cope with group change so:
# group nogroup
persist-key
persist-tun
mute-replay-warnings
<ca>
—–BEGIN CERTIFICATE—–
—–END CERTIFICATE—–
</ca>
<cert>
—–BEGIN CERTIFICATE—–
—–END CERTIFICATE—–
</cert>
<key>
—–BEGIN PRIVATE KEY—–
—–END PRIVATE KEY—–
</key>
<tls-auth>
—–BEGIN OpenVPN Static key V1—–
—–END OpenVPN Static key V1—–
</tls-auth>
key-direction 1
auth SHA512
remote-cert-tls server
cipher AES-256-CBC
comp-lzo
# end configuration
If you are using a commercial VPN service rather than your own OpenVPN endpoint, then your provider should give you configuration files much like those above. As I mentioned earlier, beware of “binary blob” non-text configurations.
If your router is anything like mine, you will need to upload the configuration file using the administrative web interface and then activate it. My router allows several different configurations to be stored so that I can vary my VPN endpoints depending on where I wish to pop up on the net. Of course this means that I have to pay for several different VPSs to run OpenVPN on, but at about 3 euros a month for a suitable server, that is not a problem. I choose providers who:
- are not UK based or owned;
- have AUPs which allow VPN usage (it helps if they are also Tor friendly);
- have datacentre presences in more than one location (say Germany, as well as the Ukraine);
- allow installation of my choice of OS;
- have decent reputations for connectivity and uptime; and
- are cheap.
Whilst this may appear at first sight to be problematic, there are in fact a large number of such providers dotted around Europe. Be aware, however, that many small providers are simply resellers of services provided by other, larger, companies. This can mean that whilst you appear to be using ISP “X” in, say, Bulgaria, you are actually using servers owned and managed by a major German company or at least are on networks so owned. Be careful and do your homework before signing up to a service. I have found the lowendtalk site very useful for getting leads and for researching providers. The lowendbox website is also a good starting point for finding cheap deals when you want to test your setup.
Now go take back your privacy.
Notes
Some of the sites I found useful when considering my options are listed below.
Check your IP address and the DNS servers you are using at check2ip.com
Also check whether you are leaking DNS requests outside the tunnel at ipleak.net.
You can also check for DNS leakage at dnsleaktest.
PrivacyTools.io is a very useful resource – and not just for VPN comparisons
cryptostorm.is/ and Mullvad.net look to be two of the better paid for commercial services.
TheBestVPN site offers a VPN Comparison and some reviews of 20 providers.
A very thorough comparison of 180 different commercial VPN providers is given by “that one privacy guy“. The rest of his (or her) site is also well worth exploring.
[Edit at 3 March 2023 – The site owned originally by “that one privacy guy” referenced above seems to have been taken over by a commercial entity a couple of years ago. It no longer offers what I would call an independent view of VPN resources, merely one more list of “top ten VPNs” and, worse, contains obvious affiliate links to commercial VPN providers. I leave the reference here for historical reasons, but I would no longer recommend it as a useful resource. I have, however, deleted it from my “privacy and anonymity” links.]
Brian Krebs discusses VPN options.
Ars Technica discusses the “Impossible task of creating a best VPN list”.