Back in early 2019, I wrote about a problem I was having with mail from my system going to BT based accounts. At the time, BT was rejecting my mail as potential spam. As I wrote at the time, I was pleasantly surprised when the BT postmaster replied positively to my request that they investigate the problem. Even better, after investigation they acknowledged that the problem lay at their end and they then fixed it.
I am now having a problem with mail to an ntlworld address (@ntlworld.com), part of the virginmedia empire. But this time I have no possibility of getting their postmaster to do anything. Why? Because mail to their postmaster is also refused.
I first noticed the problem only a month or two ago. Here again, email from me to that same group of friends I wrote about in the BT scenario was being refused to one member of the group. That member has an ntlworld account, and has had for as long as he has been on the mailing list, so they must have changed their mail receipt policy recently. The ntlworld system now refuses all mail from my mailserver. The mail is apparently refused because they believe my mail server is not trustworthy.
Continue reading
Permanent link to this article: https://baldric.net/2020/10/27/braindead-mail-service/
We here in England must now limit our social interaction to the “rule of six”. Our dear, delusional, demented, certifiable, mendacious, law breaking Prime Minister says that I cannot meet in my home with more than six people – despite the fact that I can go to the Gym, or a Supermarket, or a Pub, or a Restaurant which will be inside, and with more than six people present.
Well, guess what, my grandchildren come to dinner with my wife and I and visit fairly regularly. They love their Nana. Together with their parents that makes seven people in my home.
So, I tell you now Prime Minister, I fully intend to break the law in a very “specific and limited way” (TM).
Permanent link to this article: https://baldric.net/2020/09/11/laws-are-made-to-be-broken/
My previous two posts discussed the need for encrypted DNS and then how to do it on a linux desktop. I do not have any Microsoft systems so I have no idea how to approach the problem if you use any form of Windows OS, nor do I have any Apple devices so I can’t provide advice for iOS either, but I do use Android devices. All my mobile phones for some time have been re-flashed to run a version of Android’s OS software. My current mobile (and two previous ones) run lineageOS, earlier phones used the (now discontinued) cyanogenmod ROM. I dislike google’s cavalier approach to user privacy, but I do like the flexibility and usability provided by modern smartphones. Apple devices strike me as hugely overpriced and I have never been convinced by the “oooh shiny” adoration shown by some of Apple’s hardened admirers. But each to their own.
Continue reading
Permanent link to this article: https://baldric.net/2020/06/06/encrypting-dns-on-android/
In my last post I explained that in order to better protect my privacy I wanted to move all my DNS requests from the existing system of clear text requests to one of encrypted requests. My existing system forwarded DNS requests from my internal dnsmasq caching servers to one of my (four) unbound resolvers and thence onward from them to the root or other authoritative servers. Whilst most of my requests would be shielded from prying eyes by my use of openVPN tunnels, unfortunately, this still left my requests to upstream servers from my unbound resolvers subject to snooping. I don’t like that and the opportunity to encrypt my requests using the new standard DNS over TLS (DoT) looked attractive.
This post describes how I made that change.
Continue reading
Permanent link to this article: https://baldric.net/2020/05/25/encrypting-dns-with-dnsmasq-and-stubby/
Any casual reader of trivia will be aware that I care about my privacy and that I go to some lengths to maintain that privacy in the face of concerted attempts by ISPs, corporations, government agencies and others to subvert it. In particular I use personally managed OpenVPN servers at various locations to tunnel my network activity and thus mask it from my ISP’s surveillance. I also use Tor (over those same VPNs), I use XMPP (and latterly Signal) for my messaging and my mobile ‘phone is resolutely non-google because I use lineageos‘ version of android (though that still has holes – it is difficult to be completely free of google if you use an OS developed by them). Unfortunately my email is still largely unprotected, but I treat that medium as if it were correspondence by postcard and simply accept the risks inherent in its use. I like encryption, and I particularly like strong encryption which offers forward secrecy (as is provided by TLS, and unlike that offered by PGP) and will therefore use encryption wherever possible to protect my own and my family member’s usage of the ‘net.
Continue reading
Permanent link to this article: https://baldric.net/2020/05/06/encrypting-dns/
Since my previous post below, I have been reading up on Zoom as a company, its staffing and its worrying security (or rather lack of) track record. When I wrote the initial post I said that “Zoom is a US company funded almost entirely by venture capital. Its servers are US based.”. It appears that is not entirely accurate. Indeed, it would appear that some of its servers are actually based in China, furthermore, a large number of its development staff are Chinese nationals, also based in China. And the CEO, Eric S Yuan grew up in China. On a Zoom blog post dated 26 February of this year Yuan wrote:
“I grew up in the eastern Shandong Province of China and studied at the Shandong University of Science & Technology. It’s a place I still hold dear. I am continuously inspired by the courageous efforts of those treating patients in China and around the world — working hard to try to further prevent the spread of the virus.”
Continue reading
Permanent link to this article: https://baldric.net/2020/04/10/zooming-in-on-china/
On Tuesday of this week, Boris Johnson tweeted a picture of what he called the UK’s “first ever digital Cabinet”. That picture (copy below) shows that the Cabinet meeting was held using Zoom – the sort of video conferencing software which is currently popular with business users forced to work at home during the Covid19 pandemic.

Continue reading
Permanent link to this article: https://baldric.net/2020/04/03/zooming-in-on-cabinet/
Tom Scott is a young educational entertainer who publishes fairly regularly on youtube. Back in mid 2004, whilst still a linguistics student at York, he managed to upset both the Home Office and the Cabinet Office by publishing a Department of Vague Paranoia website spoofing the rather po faced official “Preparing for Emergencies” site. Tom’s website is still in operation – unlike the official one. I guess Tom never aspired to a career in the Civil Service.
Continue reading
Permanent link to this article: https://baldric.net/2020/03/11/beware-the-zombie-apocalypse/
Well, I don’t think so. But for a while I was not entirely sure.
Following the move last November of trivia from a VM on UK2’s datacentre in London to our new home on a faster VM on ITLDC’s network I have been making a variety of minor changes and doing some essential housework. One of the biggest changes of course (fortunately for me as it turns out) was the complete separation of my two main services (mail and web) onto different VMs in different countries. My mailserver is now housed in Nuremburg where I have made some additional changes (for example I now run opendkim on it). This VM in Prague now houses just my webserver and of course is home to this blog.
Continue reading
Permanent link to this article: https://baldric.net/2020/02/27/have-i-been-pwned/
My move of trivia to a new VM last December prompted me to look again at my server configuration. In particular I wanted to ensure that I was properly redirecting all HTTP requests to HTTPS and that the ciphers and protocols I support are as up to date and strong as possible. Mozilla offers a very good security reference site which should be your first port of call if you care about server side security. The “cheat sheet” on that site gives pointers to existing good practice guidelines for most of the configuration options you should care about on a modern website. I have implemented as many of these as is possible on trivia – but I am hampered slightly by the fact that I still use WordPress as my blogging platform. WordPress (and its myriad plugins) still does lots of things I don’t actually like (such as setting cookies I can’t control, loading google fonts etc.) but I’m stuck with that unless I change platform (which I might).
Continue reading
Permanent link to this article: https://baldric.net/2020/01/22/tls-certificate-checks/
For the past four years or so I have been receiving increasingly frequent requests for either guest posts, or links to external sites (or sometimes both). The requests have increased in number ever since I started posting about my use of OpenVPN. Many of these requests want me to point to their commercial VPN site. The requests all look something like this:
Hi.
My name is Foo. I represent Bar. I found your blog on google and read your article on “X”. I think your readers will like our discussion about “X” on our site. Would you be willing to host a guest post by us, or one of our affiliates, promoting the use of “Y”? It would also be really good if you could link to our site from your article.
We are really flexible, so we could totally negotiate about special deals.
Continue reading
Permanent link to this article: https://baldric.net/2020/01/14/do-not-ask-me-for-guest-posts-or-links/
I first started using Linksys NSLU2s (aka “slugs”) in early 2008. Back then I considered them quite useful and I even ran webservers and local apt-caches on them. But realistically they are (and even then, were) a tad underpowered. Worse, since Debian on the XScale-IXP42x hasn’t been updated for several years, the slugs are probably vulnerable to several exploits. The latest version of Debian available for the slugs is probably that which I have running (“uname -a” shows “Linux slug 3.2.0-6-ixp4xx #1 Debian 3.2.102-1 armv5tel”).
Continue reading
Permanent link to this article: https://baldric.net/2020/01/14/retiring-the-slugs/
As of today we are now fully functional in our new home in a datacentre in Prague. We also have a new letsencypt certificate. If you see any problems, let me know at the usual email address.
Enjoy
Permanent link to this article: https://baldric.net/2019/12/05/welcome-to-prague/
I have been using services from ITLDC for about three years now. I initially picked one of their cheap VMs based in the Netherlands whilst I was expanding my VPN usage, and frankly, I was not expecting much in the way of customer service or assistance for the very low price I paid. After all I thought, you can’t expect much for under 3 euros a month. But I was pleasantly surprised to find that not only was the actual service pretty rock solid, but so was the help I received on the one or two occasions I had a problem. In fact I have never had to wait more than a few minutes for a response to a ticket. That is exceptional in my experience. For the last year or more, I have been using one of their VMs as an unbound DNS server and VPN endpoint.
So when I was considering a new VM I was very pleasantly surprised to note that ITLDC were offering a huge discount on new servers as part of a “black friday” promotion. I have now paid for a new debian server, based in Prague. That VM is one of their 2 Gig SSD offerings (2 Gb RAM, dual core, 15 Gb disk and unlimited traffic). Even at their normal undiscounted rate that would only have cost me 65.99 euros for a year. I paid the princely sum of 26.39 euros – a 60% discount.
Absolutely astounding value for money. Go get one before the offer runs out.
Permanent link to this article: https://baldric.net/2019/11/28/a-bargain-vps/

God help us all.
Permanent link to this article: https://baldric.net/2019/07/23/fsckd/
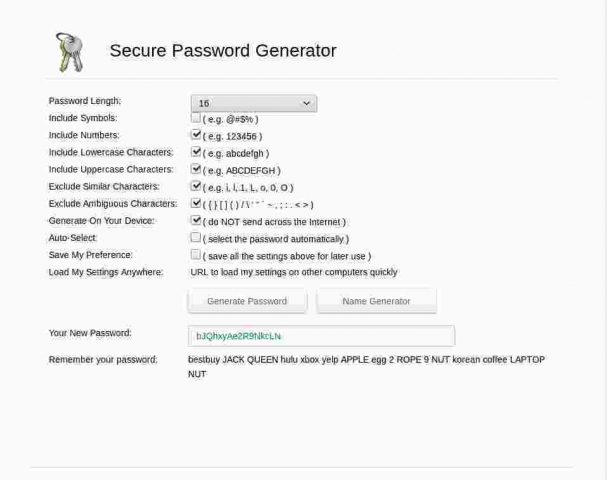
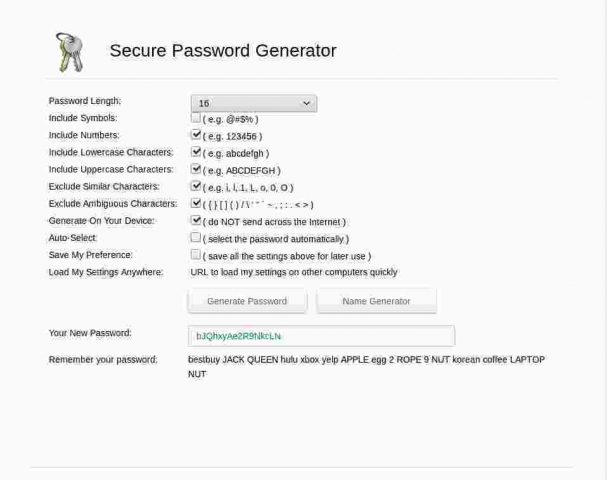
A recent exchange of email with an old friend gave me cause to revisit on-line password/passphrase generators. I cannot for the life of me imagine why anyone would actually use such a thing, but there are a surprisingly large number out there. On the upside, most of these now seem to use TLS encrypted connections so at least the passwords aren’t actually passed back to the requester in clear, but the downside is that most generators are still woefully stupid.
I particularly liked this bonkers example:
Continue reading
Permanent link to this article: https://baldric.net/2019/07/15/more-password-stupidity/
At the tail end of last year, Crispin Robinson and Ian Levy of GCHQ published a co-authored essay on “suggested” ways around the “going dark problem” that strong encryption in messaging poses Agencies such as GCHQ and its (foreign) National equivalents. In that essay, the authors were at pains to state that they were not in favour of weakening strong encryption, indeed they said:
The U.K. government strongly supports commodity encryption. The Director of GCHQ has publicly stated that we have no intention of undermining the security of the commodity services that billions of people depend upon and, in August, the U.K. signed up to the Five Country statement on access to evidence and encryption, committing us to support strong encryption while seeking access to data. That statement urged signatories to pursue the best implementations within their jurisdictions. This is where details matter, so with colleagues from across government, we have created some core principles that will be used to set expectations of our engagements with industry and constrain any exceptional access solution. We believe these U.K. principles will enable solutions that provide for responsible law enforcement access with service provider assistance without undermining user privacy or security.
Continue reading
Permanent link to this article: https://baldric.net/2019/07/10/add-my-name-to-the-list/
In my 2017 article on using OpenVPN on a SOHO router I said: “In testing, I’ve found that using a standard OpenVPN setup (using UDP as the transport) has only a negligible impact on my network usage – certainly much less than using Tor.”
That was true back then but is unfortunately not so true now.
In 2017 my connection to the outside world was over a standard ADSL line. At its best, I saw around 11 – 12 Mbit/s. Using OpenVPN on my new Asus router I saw this drop to about 10 Mbit/s. I found that acceptable and assumed that it was largely caused by the overhead of encapsulation of TCP within UDP over the tunnel.
Not so.
Continue reading
Permanent link to this article: https://baldric.net/2019/07/07/openvpn-clients-on-pfsense/
I have written about my use of OpenVPN in several posts in the past, most latterly in May 2017 in my note about the Investigatory Powers (IP) Bill. In that post I noted that all the major ISPs would be expected to log all their customers’ internet connectivity and to retain such logs for so long as is deemed necessary under the Act. In order to mitigate this unwarranted (and unwanted) surveillance as much as possible, I wrap my connectivity (and that of my family and any others using my networks) in an OpenVPN tunnel to one of several endpoints I have dotted about the ‘net. This tunnel shields my network activity from prying eyes at my ISP, but of course does not stop further prying eyes at the network end point(s). Here I am relying on the fact that my use of VMs in various European datacentres, and thus outside the scope of the IP Act, will give me some protection. But of course I could be wrong – and as I pointed out in my comparison of paid for versus roll your own VPNs, “there is no point in having a “secure” tunnel if the end server leaks like a sieve or is subject to surveillance by the server provider – you have just shifted surveillance from the UK ISP to someone else.”
Continue reading
Permanent link to this article: https://baldric.net/2019/06/26/one-unbound-and-you-are-free/
Having just returned from a family holiday which included too much food and drink and nowhere near enough exercise (well, that’s what holidays are for) I needed to get back to the gym in order to work off some of the excess. My local gym has recently undergone a major refurbishment and equipment upgrade and some of the workstations (notably the treadmills) now have integrated touch screens providing access to a variety of services. As you can see from the picture below, these services range from the obviously relevant such as details of your workout, your heartrate or linkages to fitness trackers, through TV, Youtube or Netflix access, to the less obviously necessary social media services such as Facebook, Instagram and Twitter. God knows how you can tweet and run at the same time and it is beyond me why anyone would even consider giving their social media account details to a gym company. But hey, the technology is there and people do use it.

treadmill screen
Continue reading
Permanent link to this article: https://baldric.net/2019/06/11/back-to-the-gym/
The UK Parliamentary petitions site is currently hosting what appears to be one of the most popular it has ever listed. The petition seeks to gain support for revocation of article 50 so that the UK can remain in the EU. Personal politics aside (though in the interests of transparency I should say that I am a passionate supporter of remain) I believe that this petition, or one very like it, was inevitable given our dear PM’s completely shambolic handling of the whole brexit fiasco. Her latest “appeal” to the “tired” public to get behind her version of brexit in which she lays the blame for the delay to getting her deal over the line in the lap of MPs was probably the last straw for many. It is certainly a risky strategy because she needs the support of those very MPs to get the agreement she wants.
Continue reading
Permanent link to this article: https://baldric.net/2019/03/21/more-in-the-you-couldnt-make-it-up-dept/
OK, I admit to being dumb. I got another scam email yesterday of the same formulation as the earlier ones (mail From: me@mydomain, To: me@mydomain) attempting to extort bitcoin from me.
How? What had I missed this time?
Well, this was slightly different. Checking the mail headers (and my logs) showed that the email had a valid “Sender” address (some bozo calling themselves “susanne@mangomango.de”) so my earlier “check_sender_access” test would obviously have allowed the email to pass. But what I hadn’t considered was that the sender might then spoof the From: address in the data portion of the email (which is trivially easy to do).
Dumb, so dumb. So what to do to stop this?
Continue reading
Permanent link to this article: https://baldric.net/2019/02/16/postfix-sender-restrictions-job-not-done/
I mentioned in my previous post that I had recently received one of those scam emails designed to make the recipient think that their account has been compromised in some way and that, furthermore, that compromise has led to malware being installed which has spied on the user’s supposed porn habits. The email then attempts a classic extortion along the lines, “send us money or we let all your friends and contacts see what you have been up to.”
Continue reading
Permanent link to this article: https://baldric.net/2019/01/24/postfix-sender-restrictions/
I have been running my own mail server now for well over a decade. Whilst the actual physical hardware (or actually VPS system) may have changed once or twice during that time, the underlying software (postfix and dovecot on debian) has not really changed all that much. However, what has changed over the last decade or so, is the expectation that mail systems will be much more robust, better managed, less insecure (no more “open relays”) and harder on spam than had been the case in the early days of wide takeup of email by the public. Ignoring the “free” offerings from the likes of google, microsoft and others, it would arguably be cheaper, and certainly easier, for me to simply pay for an external mail service by one of the many providers out there. It is pretty easy to find companies offering to host personal email for about a tenner or at most twenty pounds a year. Those “solutions” (as providers seem to love to call their products) usually give you decent anti-spam, A/V scanning, POP3S/IMAPS connectivity (or if you really must, a webmail interface) and can usually alias mail to your preferred domain – particularly if you buy a domain name with your email service. But they always have limitations that I don’t like. The most obvious ones are: restrictions on the number of actual email addresses (as opposed to aliases), limited storage (though that is becoming less of a problem these days), and artificial restrictions on attachment sizes. And I’m bloody minded. I like to control my own email. I run my own email service for the same reason I manage my own DNS, run my own webservers, manage my own wordpress installation, run my own XMPP server and VPNs and manage my own domestic local network with assorted servers hanging off it. I like control and I dislike the opportunity outsourced services have for providing third parties access to my data. My personal data.
Besides, a boy needs a hobby.
Continue reading
Permanent link to this article: https://baldric.net/2019/01/23/congratulations-to-bt/